- 06/07/2023
- Personal Projects
- Hyeseon Oh
- #project, #personal
About the Project
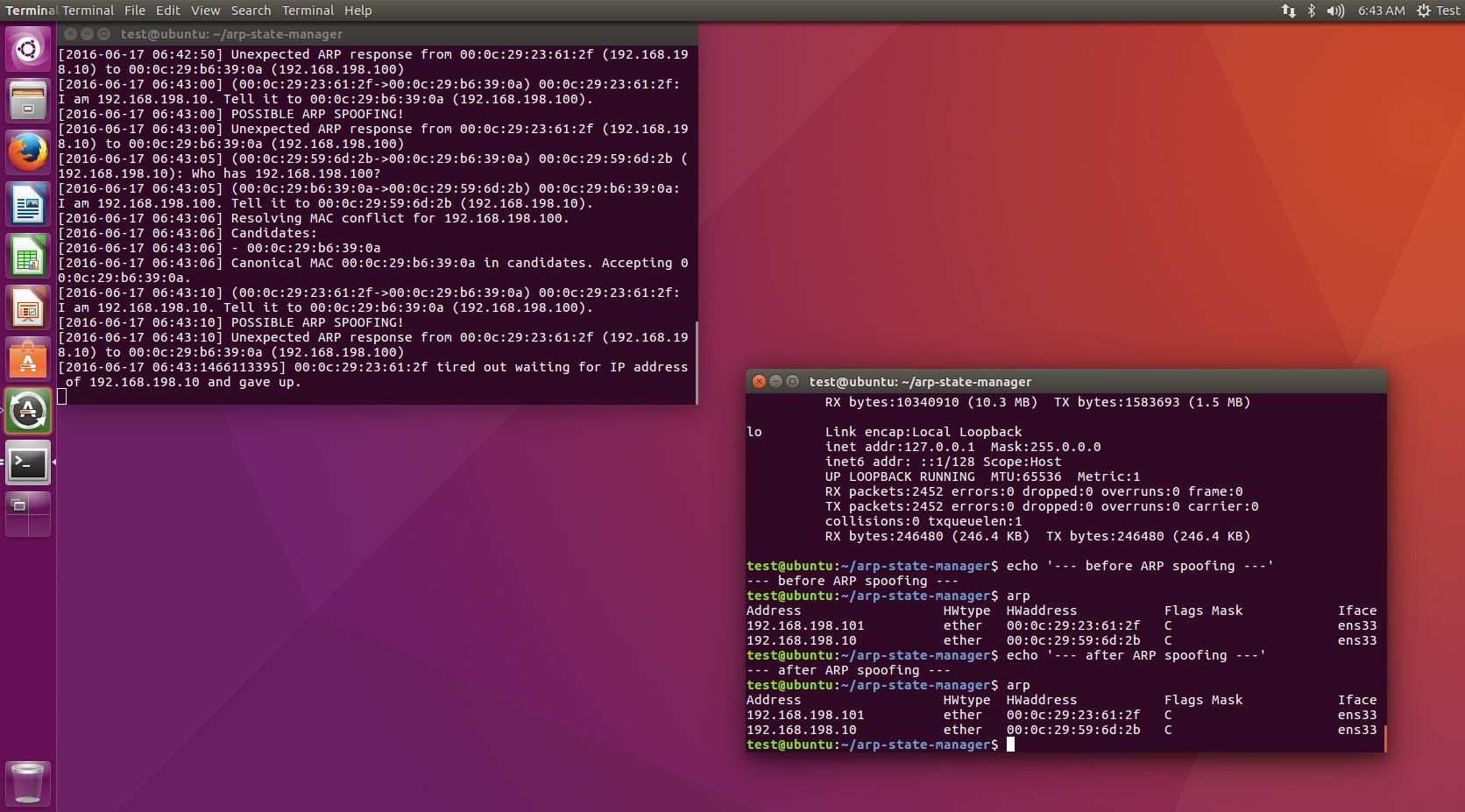
For a term project, we considered security vulnerabilities which could endanger everyday life while technically being elementary. From that perspective, we considered ARP spoofing, in which the attacker intrudes into an externally exposed server and disturb a local-area network, as our main attack scenario. We devised a scenario in which a MediaWiki vulnerability is used to deliver an ARP spoofing payload, while considering a method to defend from ARP spoofing while another machine is being compromised.
In this project, we exploited the fact that a valid owner of an IP-MAC address pair would send a gratuitous ARP packet (gARP packet) even there is no request for an ARP query. By referring to the hosts' gARP and initial ARP table before attack, we could reliably find a valid mapping between IP addresses and MAC addresses.
Response to ARP query and responses
If a client sent an ARP query, according to the answer, we react as the following: - If there is only one ARP response, we consider it as a benign scenario, passing the response to the system. - If there are multiple ARP responses but one of them belongs to the current valid mapping, we consider the rest of them as attacker(s) and ignore the response. - If there are multiple ARP response and none of them belongs to the current valid mapping, find which of the hosts sent gARP before. The host with a gARP log would be the rightful owner of the IP-MAC address pair, because sending a gARP as an attack would be a risky behavior. - Else, the scenario cannot be judged, and is reported.
Low-level implementation
Since we needed to quickly implement the prototype, we only implemented the part where we parse the input ARP packet. We instead invoked the arptables command of Linux to modify the system ARP mapping.
Figures
Contribution and Information
- Period of Development: 9/2016 ~ 12/2016
- Total Particiapnts: 2 people
- My Roles: entire programming
- Used Tech Stacks: Python, networking, Linux
Downloads
Note that the report is in Korean, and the report states my name as Kuenwhee Oh (오근휘), which was my name before change.
