- 04/07/2023
- Publications
- Hyeseon Oh
- #publication, #research
About the Paper
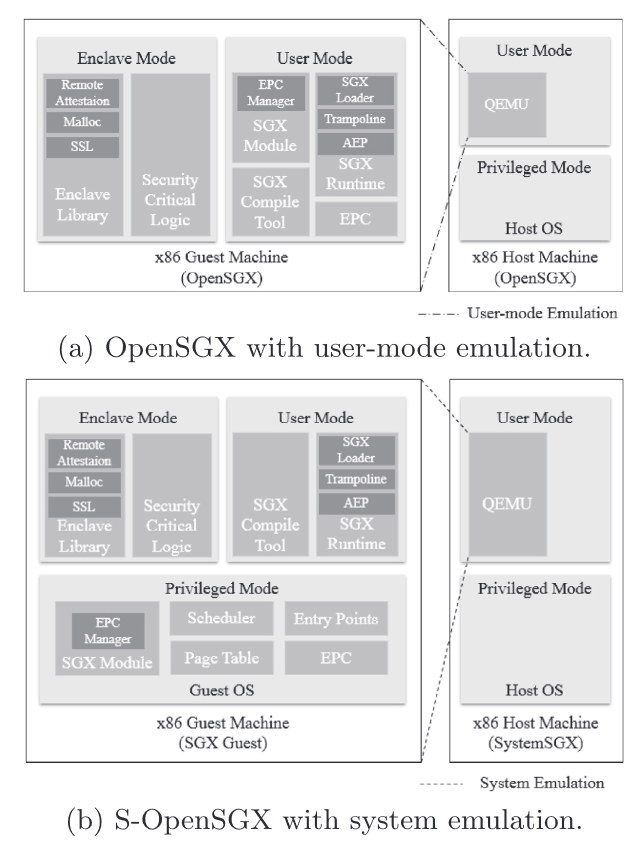
Researching the trusted execution environment (TEE) obviously requires the hardware which is equipped with the environment. This was especially harmful in case of Intel Software Guard Extensions (SGX), which was only included in a limited subset of hardware and the more recent revision of SGX V2 was not even included in an actual chip. Since this could become a barrier for academic research, there were some researches which tried to instead simulate SGX with software-level emulation. There was an existing approach called OpenSGX which used the user-level QEMU to implement SGX functionalities. However, it had some problems like not being able to run actual SGX apps because running apps on it was different from running on an actual SGX-capable processor, and full SGX emulation was fundamentally impossible because some things like page table structure could not be modified from the user-level emulation.
To overcome this issue, we took this approach one step further and strived to implement SGX capability on the system-level QEMU. From this, apps targeting actuial SGX hardware could be run, arbitrary structures could be modified, and since it emulates the entire hardware, we could go even further than the real machine like implementing SGX V2 modifications or suggesting hardware modification.
Implementing the system-level emulation was not that simple. Differences on virtual address systems, address comparison, and most importantly, implementing the SGX functionality at the transistor-level was not that easy. However, we overcame these difficulties and implemented a system-level emulation of Intel SGX. Moreover, we showed that a system-level emulation of SGX was benefactory to researchers by providing a mitigation of an attack which the vanilla SGX is vulnerable against.
Contribution and Information
- Period of Research and Writing: 9/2015 ~ 5/2017
- Contribution among Total Participants: 5th among six authos (+ a corresponding author)
- Role: Development of an emulator feature and bug fix
- Technology Used: C (QEMU, etc.)
Abstract
Intel recently introduced Software Guard Extensions (SGX) to enable applications to protect their selected code and data from privileged platform software. As it draws wider attention from the security research community, an open-source emulator for SGX (OpenSGX) has been developed to allow researchers to explore the SGX environment. To the best of our knowledge, OpenSGX is currently the only publicly available SGX emulation platform; however, its system-level support is largely limited owing to its user-mode emulation. In particular, experiments that require system functionalities or device emulation cannot be conducted with the current OpenSGX. To solve this problem, we propose System-OpenSGX (S-OpenSGX), which leverages QEMU's system emulation to provide researchers with full system-level support for exploring SGX enclave-based programming. In this paper, we show the design of S-OpenSGX, including system functionalities such as scheduling, multithreading, page table handling, and SGX paging. Non-trivial issues derived from the difference between user-mode and system emulation, and our approaches to addressing them are also described. Lastly, we utilize S-OpenSGX to experiment with a new mitigation method against the data leaking attack on enclave threads and an APIC (Advanced Programmable Interrupt Controller) device modification to reduce SGX's mode switch overhead.
